6 min read
AgenticOps: Operating Runtime-Defined Systems
David Greenberg
Chief Marketing Officer
AgenticOps is the operational discipline for building, deploying, and governing AI agents safely across the full lifecycle—from scanning tools to governing runtime execution.
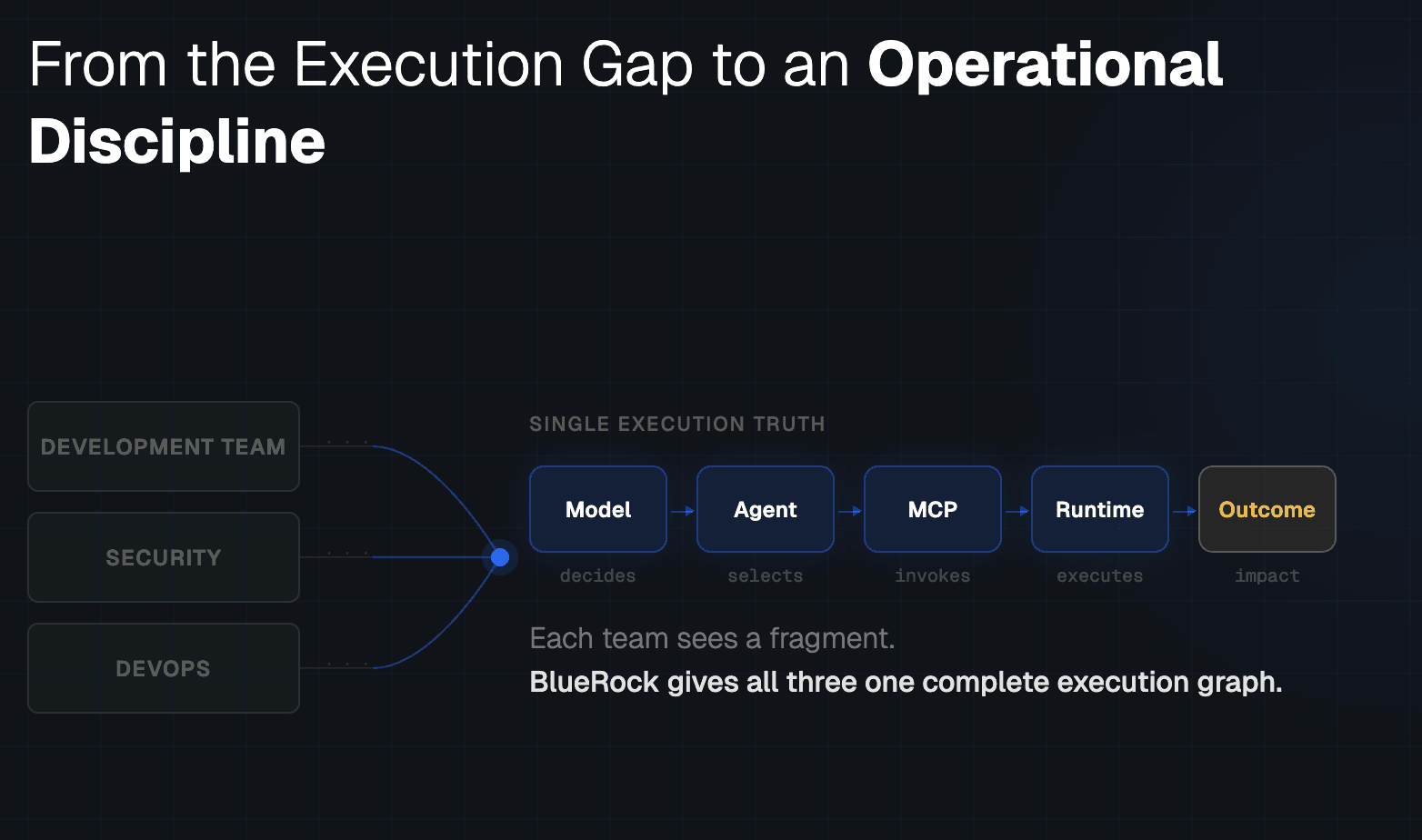
From the Execution Gap to an Operational Discipline
In Part 1, we explored a structural shift in how software behaves.
Execution paths are no longer fully defined at build time.
They are composed dynamically at runtime.
Agents interpret context.
They select tools.
They invoke MCP servers.
They coordinate with other agents.
They generate execution paths dynamically as they attempt to achieve an objective.
Traditional Systems
Code → ExecutionAgentic Systems
Code → Agent → Tool → MCP → Runtime → Impact
The resulting system behavior is not fully described in source code. It emerges during execution.
This is the Agentic Execution Gap — the growing disconnect between how agentic systems behave in production and the fragmented visibility and governance systems organizations rely on to operate them.
Logs alone cannot close this gap.
What is required is an operational model designed for systems whose behavior emerges dynamically during execution.
We call that operational discipline AgenticOps.
What AgenticOps Is
AgenticOps is the operational framework for managing runtime-defined execution across the full lifecycle of agent development and deployment.
It recognizes that agentic systems span multiple operational domains simultaneously.
Developers build the agents.
Security governs what they are allowed to do.
DevOps runs the infrastructure they operate within.
MCP server builders expose capabilities those agents rely on.
Each of these groups traditionally operates with its own tools and telemetry.
Agentic systems break that separation. Execution now crosses all of those domains in a single runtime path.
AgenticOps establishes a shared operational layer that connects these systems through:
End-to-end execution tracing
Durable identity across agents and tools
Capability classification
Runtime guardrails
Cross-team visibility
Continuous feedback loops
The goal is simple:
When agents act, the entire organization must be able to see, understand, and govern what happened.
The Agentic Action Path as the System of Record
Part 1 introduced the Agentic Action Path — the chain of decisions and actions that connect model reasoning to real-world system impact.
At runtime, that path often looks like this:
Model → Agent → MCP server → Tool → Runtime execution → Downstream system impact
AgenticOps treats this path as the primary unit of operational reasoning.
Not prompts.
Not tool calls in isolation.
Not infrastructure logs.
The complete execution graph.
When teams attempt to operate agentic systems without this unified view, they fall back on fragmented signals:
Developers analyze model traces.
Security teams review permissions.
DevOps monitors infrastructure telemetry.
MCP server builders examine server logs.
Each group sees only a portion of the story.
AgenticOps aligns these views around a single execution truth.
To do that, several capabilities become essential:
End-to-end tracing across the full action path
Persistent identity for agents and tools across systems
Correlation between tool invocation and runtime state mutation
Reconstruction of execution paths after the fact
Without this shared execution graph: Debugging becomes partial. Governance becomes abstract. Audibility becomes incomplete.
Why Agentic Systems Require a Shared Operational Surface
Agentic systems generate behavior dynamically.
A single decision can propagate across tools, services, and infrastructure in milliseconds.
One agent might call a tool that invokes a server, which triggers another system, which alters data that shapes the next decision.
This compounding behavior creates a problem for traditional operational models.
The systems responsible for building, governing, and operating software no longer observe the same execution path.
Developers see reasoning.
Security sees permissions.
DevOps sees infrastructure effects.
MCP server builders see capability invocation.
But the system itself operates across all of these layers simultaneously.
AgenticOps creates a shared operational surface where these perspectives converge.
When teams operate from the same execution graph:
Developers can trace reasoning into real system actions
Security teams can evaluate behavior in execution context
DevOps can correlate infrastructure effects with agent decisions
MCP server builders can understand how their capabilities are exercised in production
This alignment becomes essential as agentic systems move from experimentation into production workflows.
Observability Alone Is Not Enough
Agentic systems require deep observability.
But observability by itself does not constrain behavior.
AgenticOps therefore combines two capabilities:
high-resolution visibility
and
runtime control
Observability must capture more than conventional telemetry.
Agentic execution requires visibility into:
persistent agent identifiers
tool capability classifications
cross-MCP execution chains
state mutation across systems
reconstruction of dynamic execution graphs
This level of visibility allows teams to explain what happened.
But explanation alone is insufficient when agents are capable of taking consequential actions.
Control Must Bind to Execution Context
Static permission models were designed for deterministic systems.
Agentic systems behave differently.
Execution paths are composed dynamically based on the context an agent encounters during runtime.
AgenticOps therefore introduces runtime control mechanisms that bind directly to execution context:
Capability classification (read, write, destructive)
Guardrails attached to runtime identities
Sandboxed execution environments
Enforcement of build-time approvals during runtime
Real-time blocking of out-of-bounds behavior
These mechanisms ensure that control evolves alongside dynamic execution rather than attempting to restrict it with static rules. Guardrails become precise because they operate with full knowledge of the execution context surrounding each action.
The AgenticOps Lifecycle
Agentic systems cannot be governed solely during deployment.
They must be managed across the entire lifecycle of development and operation.
AgenticOps therefore spans five stages.
1. Scan
Before integration, organizations must understand the capabilities agents will interact with.
This includes:
Evaluating MCP servers
Classifying tool capabilities
Identifying destructive interfaces
Maintaining structured registries of capabilities
A trust registry becomes foundational at this stage.
It establishes identity and operational attributes for the components agents depend on.
2. Build
During development, these attributes become part of the system itself.
Teams attach metadata to tool interfaces. Capability constraints are bound to agents. CI policies enforce risk classifications. Build-time intelligence becomes runtime context.
3. Test
Testing must reflect the dynamic nature of agentic systems.
Rather than validating deterministic paths, teams simulate dynamic execution patterns:
multi-tool invocation
MCP propagation
guardrail enforcement
identity persistence
Testing becomes a process of evaluating how execution behaves across possible paths.
4. Deploy
Deployment no longer marks the end of system definition.
It marks the beginning of runtime accountability.
At this stage:
identity metadata is preserved
guardrails are activated
execution graphs become the system of record
The system is now capable of explaining how it behaves.
5. Run
During runtime operation, AgenticOps becomes continuous.
Teams:
trace the evolving Agentic Action Path
detect authority expansion
identify anomalous tool chains
refine guardrails based on observed behavior
The lifecycle becomes an ongoing loop:
Scan → Build → Test → Deploy → Execute → Observe → Refine
AgenticOps as an Operating Model
AgenticOps is not a product category. It is an operating model for runtime-defined systems. It formalizes three requirements for operating agentic software at scale:
Execution-level visibility
Cross-team operational alignment
Runtime governance
In traditional software systems, the primary challenge was intelligence.
In agentic systems, the primary challenge becomes execution.
Organizations that recognize this shift will not simply build agents.
They will build the operational systems required to manage them.
Closing
Autonomy will continue to expand.
Agents will coordinate with other agents.
Tool ecosystems will grow.
Execution paths will become increasingly dynamic.
The organizations that succeed in this environment will not necessarily deploy more agents.
They will deploy agents whose execution they can:
Trace.
Explain.
Constrain.
Continuously improve.
That capability — the ability to operate runtime-defined systems — is the foundation of AgenticOps.
FAQ
What is AgenticOps?
AgenticOps is the operational framework for managing runtime-defined execution across the full lifecycle of AI agent development and deployment. It establishes a shared operational layer connecting developers, security, DevOps, and MCP server builders through end-to-end execution tracing, durable identity, capability classification, and runtime guardrails.
How is AgenticOps different from traditional observability?
Traditional observability reconstructs what happened after execution. AgenticOps combines high-resolution visibility with runtime control — capturing the full Agentic Action Path while also enforcing guardrails that bind directly to execution context. Observability explains; AgenticOps explains and constrains.
What is the AgenticOps lifecycle?
The AgenticOps lifecycle spans five stages: Scan (evaluate MCP servers and classify tool capabilities), Build (attach metadata and capability constraints), Test (simulate dynamic execution patterns), Deploy (activate guardrails and preserve identity metadata), and Run (continuously trace, detect anomalies, and refine constraints). It operates as a continuous loop: Scan, Build, Test, Deploy, Execute, Observe, Refine.
What is the Agentic Action Path?
The Trust Context Engine integrates directly into CI/CD pipelines, allowing teams to classify tools, attach trust metadata, and establish governance signals during build and deployment. Developers can move quickly with confidence that trusted context is already in place before agents reach production systems — without requiring manual review at runtime.
The Agentic Action Path is the complete runtime execution chain: Model to Agent to MCP server to Tool to Runtime execution to Downstream system impact. AgenticOps treats this path as the primary unit of operational reasoning and the system of record for agent behavior — not prompts, not tool calls in isolation, but the full execution graph.
Why do agentic systems need a shared operational surface?
Agentic execution crosses multiple domains simultaneously — dev, security, infrastructure, and MCP servers. Each team traditionally operates with its own tools and telemetry, but agents generate behavior that spans all of these layers in a single runtime path. Without a shared operational surface, teams reason from fragmented signals and cannot coordinate effectively.