Guardrails For The Full Agentic Action Path
Apply precise control across tools, MCP servers, and downstream runtime actions using the signals attached to each step of execution.
Agents determine behavior during execution — selecting tools, invoking MCP servers, and triggering downstream actions across connected components.
BlueRock applies guardrails where that behavior actually occurs, using Trust Context to evaluate what is being invoked, which capabilities are being used, and whether execution should proceed.
Instead of relying on static approvals, gateway rules, or coarse access controls, BlueRock enables policies that operate directly on the Agentic Action Path.
That gives engineering, DevOps, and security teams a more precise way to govern agent behavior in production — without blocking safe execution or slowing development.
The Problem
Agentic Execution Breaks Traditional Governance Models
Instead of relying on static approvals, gateway rules, or coarse access controls, BlueRock enables policies that operate directly on the Agentic Action Path.
That gives engineering, DevOps, and security teams a more precise way to govern agent behavior in production — without blocking safe execution or slowing development.
Key Capabilities
BlueRock applies guardrails directly to execution — giving teams a precise way to guide agent behavior as it unfolds across tools, MCP servers, and downstream actions.
These capabilities are powered by the Trust Context Engine, which attaches the signals needed to evaluate execution at each step of the Agentic Action Path.
How It Works
Guardrails for agent behavior as execution unfolds across the Agentic Action Path.
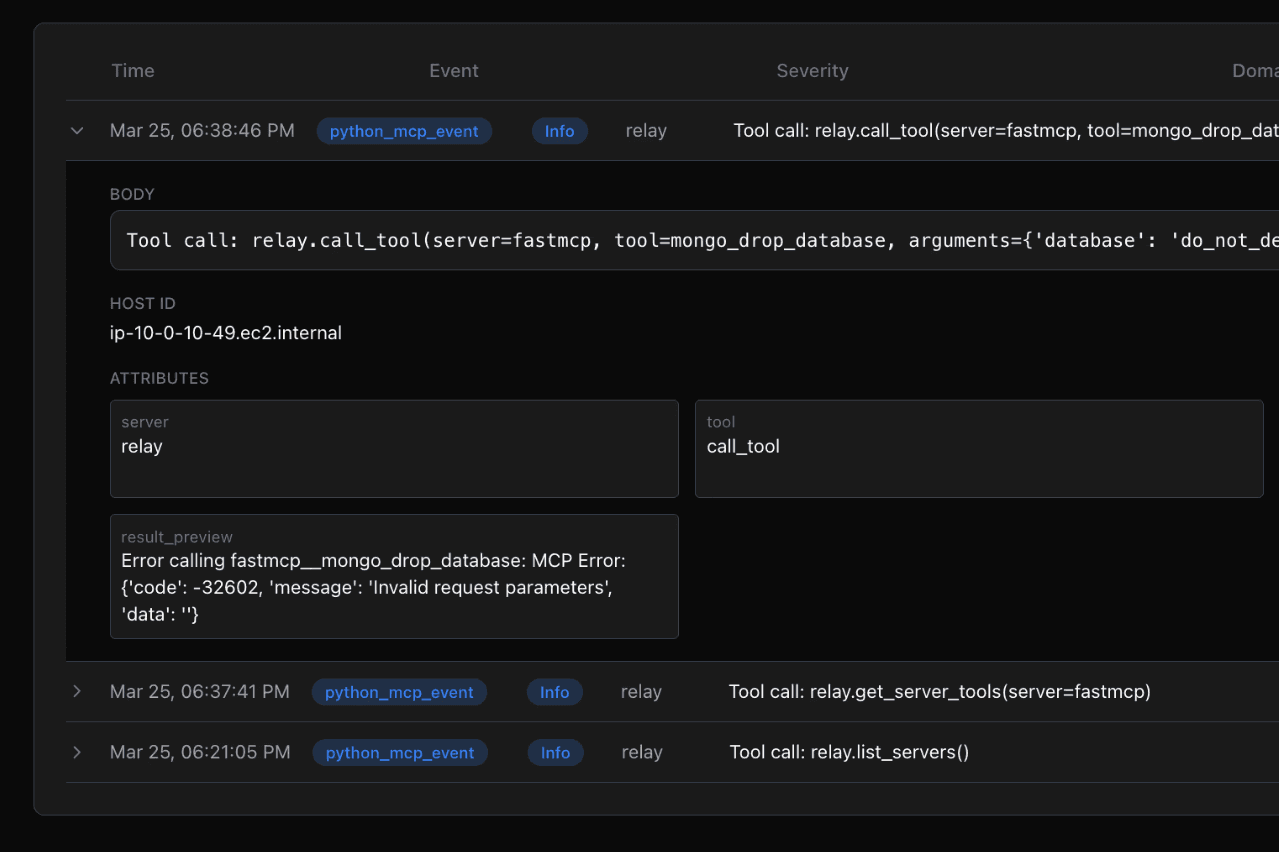
The Trust Context Engine continuously captures signals from two sources: curated MCP trust data from the MCP Trust Registry and real-time execution signals captured by BlueRock sensors.
These signals are attached to each step of the Agentic Action Path — from agent decision to tool invocation, MCP server interaction, and downstream action — creating a complete view of what is being executed.
Guardrails evaluate each step as it occurs, using those signals to determine whether execution should proceed, be constrained, or be blocked based on what is actually being invoked.
As execution propagates across tools and MCP servers, policies apply consistently across the full path — enabling precise control over how behavior unfolds in production.
To see how the Agent Action Paths are visualized, explore Agentic Observability →
To understand how Trust Context powers guardrails, see the Trust Context Engine →
Common Questions
Everything you need to know about BlueRock Real-time Guardrails.
How are BlueRock guardrails different from traditional API gateways?
Gateways inspect requests at system boundaries — but agent execution rarely happens at a single boundary. BlueRock guardrails operate directly on the Agentic Action Path, applying controls as execution propagates across tools, MCP servers, and downstream systems in real time. By the time a gateway sees a request, the chain may already be in motion.
What context do guardrails use to make enforcement decisions?
Guardrails are powered by the Trust Context Engine, which provides real-time execution context including agent identity, tool capabilities, MCP server trust attributes, and runtime conditions. This allows policies to adapt dynamically to what's actually happening during execution — not just what was anticipated at policy definition time.
Do guardrails slow down agent development or require changes to existing workflows?
No. BlueRock enforces guardrails during execution without requiring developers to change their frameworks, IDEs, or tooling. Teams retain full development velocity while security and operations teams gain runtime control.
Can guardrails govern behavior across multiple tools and MCP servers within a single agent run?
Yes. Controls follow execution across the full Agentic Action Path — spanning tools, MCP servers, data systems, and infrastructure — rather than being scoped to a single checkpoint. Organizations can define operational boundaries that apply wherever execution travels.
How do guardrails relate to Agentic Observability?
They work together. Agentic Observability gives teams visibility into how execution propagates across systems. Guardrails act on that same execution context to allow, constrain, or block actions in real time. Together, they provide both the visibility and the control needed to govern agentic behavior at scale.